Decode AVR Microcontroller ATMEL ATmega1280
Decode AVR Microcontroller ATMEL ATmega1280 is a professional technical service aimed at recovering and replicating embedded firmware from legacy and industrial control systems built around the powerful ATmega1280. This high-performance AVR microcontroller integrates 128KB of Flash program memory, 8KB SRAM, and 4KB EEPROM, together with multiple UART interfaces, SPI, I²C (TWI), 16-channel ADC, timers, PWM outputs, and advanced interrupt architecture. As a feature-rich MCU, the ATmega1280 has been widely deployed in industrial automation controllers, robotics systems, medical instruments, automotive diagnostic tools, 3D printers, and communication gateways. Its large memory capacity and stable AVR core make it ideal for complex firmware applications that require reliable data processing and real-time control. However, when original firmware source code or project archives are lost, decoding and cloning the binary file from a secured chip becomes essential for maintenance and reproduction.
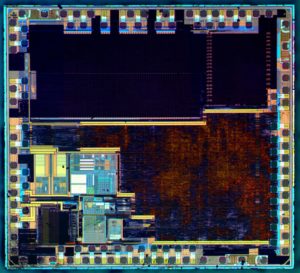
In many real-world cases, the ATmega1280 microcontroller is configured as a secured, protected, or locked MCU, with fuse bits and lock bits enabled to prevent unauthorized access to its Flash and EEPROM memory. Under such conditions, standard programmers cannot simply read, copy, or dump the firmware binary, heximal file, or program archive. Our Decode AVR Microcontroller ATMEL ATmega1280 service focuses on safely crack, unlock, decrypt, and replicate the encrypted firmware stored inside the chip. The objective is to recover the complete binary data archive—including Flash program memory, EEPROM configuration file, and calibration parameters—without altering the integrity of the microprocessor. By performing a controlled firmware dump and reconstructing the binary file, we can replicate the MCU program image even when the device is locked or encrypted. This process allows clients to restore a missing source code baseline, rebuild a functional firmware archive, and copy the program data into new replacement chips. Concentrating on binary extraction, memory recovery, and decryption of protected data ensures that the cloned microcontroller operates identically to the original secured unit.
Endurance: Up to 64K Bytes Optional External Memory Space
JTAG (IEEE std. 1149.1 compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescaler and Compare Mode
– Four 16-bit Timer/Counter with Separate Prescaler, Compare- and Capture Mode
– Real Time Counter with Separate Oscillator

– Four 8-bit PWM Channels
– Six/Twelve PWM Channels with Programmable Resolution from 2 to 16 Bits
(ATmega1281/2561, ATmega640/1280/2560)
– Output Compare Modulator
– 8/16-channel, 10-bit ADC (ATmega1281/2561, ATmega640/1280/2560)
– Two/Four Programmable Serial USART (ATmega1281/2561,ATmega640/1280/2560)
– Master/Slave SPI Serial Interface
– Byte Oriented 2-wire Serial Interface
– Programmable Watchdog Timer with Separate On-chip Oscillator
– On-chip Analog Comparator
– Interrupt and Wake-up on Pin Change
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated Oscillator
– External and Internal Interrupt Sources
– Six Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, Standby, and Extended Standby I/O and Packages
– 54/86 Programmable I/O Lines (ATmega1281/2561, ATmega640/1280/2560)
– 64-pad QFN/MLF, 64-lead TQFP (ATmega1281/2561)
– 100-lead TQFP, 100-ball CBGA (ATmega640/1280/2560)
– RoHS/Fully Green
Temperature Range:
– -40°C to 85°C Industrial
Ultra-Low Power Consumption
– Active Mode: 1 MHz, 1.8V: 500 µA
– Power-down Mode: 0.1 µA at 1.8V
Speed Grade:

– ATmega640V/ATmega1280V/ATmega1281V:
0 – 4 MHz @ 1.8 – 5.5V, 0 – 8 MHz @ 2.7 – 5.5V
– ATmega2560V/ATmega2561V:
0 – 2 MHz @ 1.8 – 5.5V, 0 – 8 MHz @ 2.7 – 5.5V
– ATmega640/ATmega1280/ATmega1281:
0 – 8 MHz @ 2.7 – 5.5V, 0 – 16 MHz @ 4.5 – 5.5V
– ATmega2560/ATmega2561:
0 – 16 MHz @ 4.5 – 5.5V
Technically, attempting to break the protection of a locked ATmega1280 chip involves multiple engineering challenges. The security architecture of this MCU may trigger automatic erase procedures if improper read commands are issued. Voltage instability, aging Flash cells, corrupted EEPROM segments, or partially damaged memory blocks can further complicate the firmware dump procedure. Additionally, encrypted or protected configurations often hide critical program sections, making direct binary extraction impossible through conventional ISP interfaces. Because of these risks, decoding a secured AVR microcontroller requires precise control, non-destructive analysis, and strict data validation to ensure that the recovered firmware file is complete and accurate. The complexity of unlocking such a microprocessor explains why professional decoding is necessary when production continuity depends on it.

From a strategic perspective, the ability to decode AVR microcontroller ATMEL ATmega1280 devices delivers substantial benefits to manufacturers and system integrators. By recovering and decrypting the firmware binary archive from a protected chip, clients can replicate discontinued products, maintain long-term supply chains, and avoid costly redesign of hardware platforms. Restoring the original program memory and EEPROM data allows accurate duplication of the MCU, ensuring compatibility with existing system architecture. For industries relying on stable embedded control systems, cloning a locked microcontroller safeguards intellectual investment, reduces downtime, and extends product lifecycle. Ultimately, decoding and replicating a secured ATmega1280 transforms inaccessible firmware data into a recoverable engineering asset, supporting sustainable production and reliable after-sales service.
