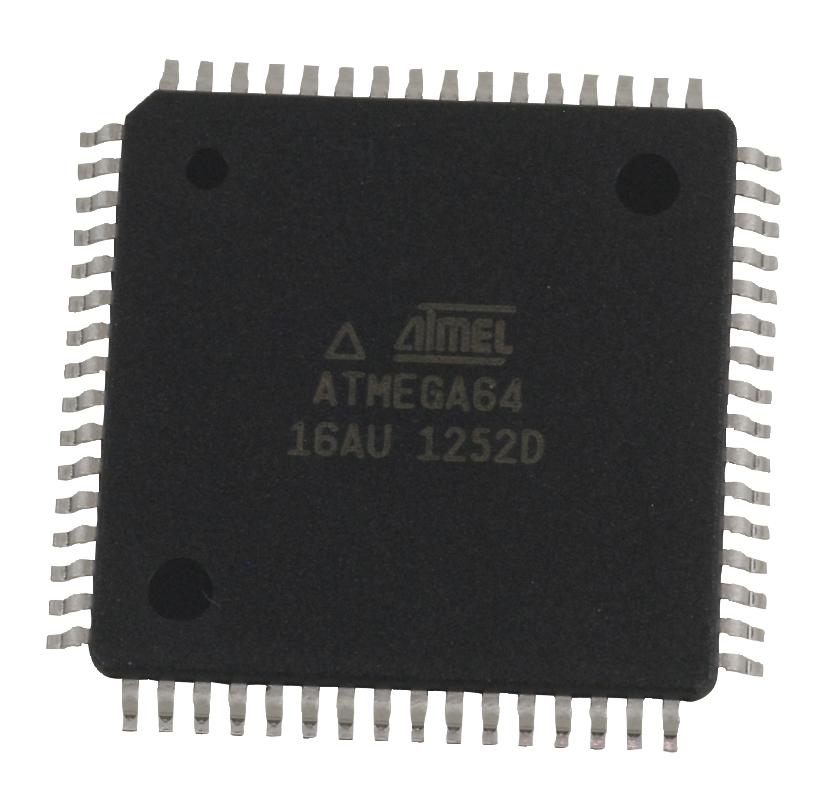
Attack AVR MCU ATmega64L
The ATmega64L is a high-performance, low-power 8-bit AVR microcontroller (MCU) developed by Microchip Technology. It features enhanced RISC architecture, extensive flash memory, internal EEPROM, and powerful control functions, making it a popular choice for mission-critical embedded applications such as industrial controllers, defense systems, and communication devices. Its architecture includes several layers of readout protection to secure valuable firmware, source code, and binary data. When firmware becomes inaccessible due to security locks or missing backups, engineers may need to attack AVR MCU ATmega64L to recover, restore, or duplicate the embedded program.

We can Attack AVR MCU ATmega64L, please view below features for your reference:
High-performance, Low-power Atmel® AVR® 8-bit Microcontroller
· Advanced RISC Architecture
– 130 Powerful Instructions – Most Single Clock Cycle Execution
– 32 x 8 General Purpose Working Registers + Peripheral Control Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
– Programming Lock for Software Security
– SPI Interface for In-System Programming
JTAG (IEEE std. 1149.1 Compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– Two Expanded 16-bit Timer/Counters with Separate Prescaler, Compare Mode, and
Capture Mode
– Real Time Counter with Separate Oscillator
– Two 8-bit PWM Channels
– 6 PWM Channels with Programmable Resolution from 1 to 16 Bits
– 8-channel, 10-bit ADC
8 Single-ended Channels
7 Differential Channels
2 Differential Channels with Programmable Gain (1x, 10x, 200x)
– Byte-oriented Two-wire Serial Interface
– Dual Programmable Serial USARTs
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Six Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, Standby
and Extended Standby

– Software Selectable Clock Frequency
– ATmega103 Compatibility Mode Selected by a Fuse
– Global Pull-up Disable
I/O and Packages
– 53 Programmable I/O Lines
– 64-lead TQFP and 64-pad QFN/MLF
Operating Voltages
– 2.7V – 5.5V for ATmega64L
– 4.5V – 5.5V for ATmega64
Speed Grades
– 0 – 8 MHz for ATmega64L
– 0 – 16 MHz for ATmega64
The ATmega64L offers a set of fuse bits and lock bits to implement code protection. These bits are designed to prevent readout, copy, or dump operations once enabled. In particular, the lock bits block external access to flash and EEPROM memory, while certain fuse bit configurations may permanently disable debugging or programming interfaces. This makes the device extremely secured, often classified as locked, encrypted, or protected against unauthorized extraction.
Despite these features, there are legitimate cases where users require access to the original firmware for maintenance, legacy system duplication, or disaster recovery. In such cases, unlocking or attacking the protection becomes essential—not with malicious intent, but for system continuity or migration.
The task to break, hack, or unlock the ATmega64L‘s protection system is highly technical, due to:
- Permanent Fuse Configuration – Improperly set fuse bits can disable programming and debugging modes, blocking even partial readout.
- Self-Erase Mechanisms – Some MCU configurations may auto-erase flash memory upon unauthorized access attempts, making direct dump operations difficult.
- Signal Interface Lockouts – Interfaces such as ISP or JTAG may be fully disabled, requiring alternative access routes or reverse engineering approaches.
Crucially, removing fuse bit protection without damaging the chip or corrupting the memory archive requires precise tools and high-level expertise. Physical or invasive methods such as decapsulation or chip-layer probing are sometimes considered, but must be applied with extreme caution to avoid loss of critical data.
At our lab, we provide professional support to attack AVR MCU ATmega64L in order to retrieve, decode, or replicate embedded firmware and heximal program files. Our services are tailored for companies, repair centers, and engineering teams needing access to protected microcontrollers for legitimate and compliant purposes.
We use a combination of advanced microelectronic diagnostics and non-destructive access methods to unlock the protection layers, break off fuse bit configurations, and perform full memory dump operations. Our techniques ensure safe and accurate recovery of binary files and EEPROM content, suitable for cloning, duplicating, or rebuilding legacy systems.
Tags: rotura интегрална схема entsrapted bin,rotura интегрална схема entsrapted code,rotura интегрална схема entsrapted data,rotura интегрална схема entsrapted eeprom,rotura интегрална схема entsrapted file,rotura интегрална схема entsrapted firmware,rotura интегрална схема entsrapted flash,rotura интегрална схема entsrapted hex,rotura интегрална схема entsrapted memory,rotura интегрална схема entsrapted program,rotura интегрална схема entsrapted software