IC Break Economical Effect
IC breaker can crack any chip protection provided he has enough time and resources. The question is how practical it would be. If it takes ten years to break a IC which in three years time is replaced by a successor with even better security, then the defence has won. On the other hand, the vulnerability could be buried within the design blocks itself. What if your secure system was designed from insecure components?
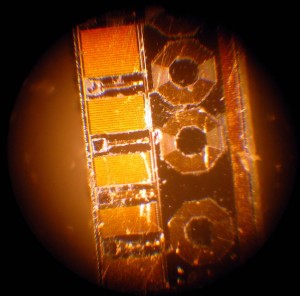
In the end, the overall security of your system is determined by the least secure element. Even if you implement a provably secure protocol, your system could be broken if the key can be easily extracted from the hardware by mechanical or optical probing. Therefore, whenever you design a secure system, proper security evaluation of all the components must be performed.
Of course it is impossible to avoid all problems; a reasonable goal is to make the process of breaking your design more expensive and time-consuming. With luck, potential IC attackers will switch to other products rather than spending money and effort on breaking your IC Chip.
Tags: чупя ic bin,чупя ic code,чупя ic data,чупя ic eeprom,чупя ic file,чупя ic firmware,чупя ic hex,чупя ic memory,чупя ic program