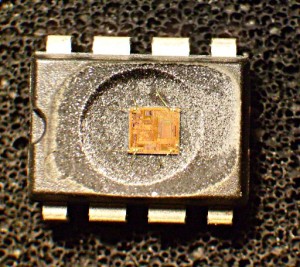
IC Chip Attacking Scenario
IC Chip Attacking Scenario can be used for different purposes depending on the goal. Sometimes copying a profitable on-the-market product include copy IC can give easy money. Larger manufacturers could consider stealing intellectual property (IP) from the device and mixing it with their own IP to disguise the theft. Others could try to steal secrets from the device either to produce a competitive product or to steal service. Product designers should first think about the possible motives for attacking ic chip their devices and then concentrate on the protection mechanisms. The following attacking scenarios should be considered during the system design.
Tags: копирам чып bin,копирам чып code,копирам чып data,копирам чып eeprom,копирам чып file,копирам чып firmware,копирам чып flash,копирам чып hex,копирам чып memory,копирам чып program